Working Together Apart (Synthesis Lectures on Human-Centered Informatics)
by Judy S. Olson and Gary Olson
Increasingly, teams are working together when they are not in the same location, even though there are many challenges to doing so successfully. Here we review the latest insights into these matters, guided by a framework that we have developed during two decades of research on this topic. This framework organizes a series of factors that we have found to differentiate between successful and unsuccessful distributed collaborations. We then review the kinds of technology options that are availab...
E-government has become a global phenomenon through its use of Internet technologies as a platform for exchanging information, providing services, and transacting with citizens, businesses, and other arms of government. E-Government Development and Diffusion: Inhibitors and Facilitators of Digital Democracy provides a comprehensive, integrative, and global assessment of the e-government evolution in terms of real-life success and failure cases. Containing research from leading international expe...
Digital libraries (DLs) have introduced new technologies, as well as leveraging, enhancing, and integrating related technologies, since the early 1990s. These efforts have been enriched through a formal approach, e.g., the 5S (Societies, Scenarios, Spaces, Structures, Streams) framework, which is discussed in two earlier volumes in this series. This volume should help advance work not only in DLs, but also in the WWW and other information systems. Drawing upon four (Kozievitch, Murthy, Park, Ya...
Multitasking in the Digital Age (Synthesis Lectures on Human-Centered Informatics)
by Gloria Mark
In our digital age we can communicate, access, create, and share an abundance of information effortlessly, rapidly, and nearly ubiquitously. The consequence of having so many choices is that they compete for our attention: we continually switch our attention between different types of information while doing different types of tasks--in other words, we multitask. The activity of information workers in particular is characterized by the continual switching of attention throughout the day. In this...
Arguing that one way of understanding cyberspace is as an attempt to realize an electronic version of heaven, this book begins with the medieval definition of the world as spiritual space. The author traces the emergence of modern physics with its emphasis on physical space, and then presents her thesis: that cyberspace, an outgrowth of modern science, nevertheless represents a return to medieval, spiritual concerns. Cyberspace posits the existence of a genuine yet immaterial world in which peop...
Enhancing Learning Through Human Computer Interaction
Enhancing Learning Through Human Computer Interaction is an excellent reference source of Human Computer Interaction (HCI) applications and designs. This premier reference source provides a complete analysis of online business training programs and e-learning in the higher education sector. It describes a range of positive outcomes for linking information management techniques, which exploit the educational benefits of Web-mediated learning in computer-supported collaborative learning. Case stud...
Emerging Pervasive and Ubiquitous Aspects of Information Systems: Cross-Disciplinary Advancements
Since the introduction and proliferation of the Internet, problems involved with maintaining cybersecurity has grown exponentially, and have evolved into many forms of exploitation. Yet, Cybersecurity has had far too little study and research. Virtually all of the Research that has taken place in cybersecurity over many years, has been done by those with computer science, electrical engineering, and mathematics backgrounds. However, many cybersecurity researchers have come to realize that to...
Gestensteuerung zur Optimierung der Informationsprozesse (Autouni - Schriftenreihe, #92)
by Anna-Charlotte Fleischmann
Anna-Charlotte Fleischmann befasst sich damit, wie moderne Technologien die Zusammenarbeit zwischen Planung und Shopfloor unterstutzen koennen. Durch neuartige Bedienmoeglichkeiten wie der Gestensteuerung sollen komplexe Planungssysteme intuitiv gestaltet werden, um Mitarbeiter der direkten Bereiche fruhzeitig in die Planung miteinzubeziehen. Die Autorin nutzt verschiedene Ansatze zur Entwicklung von Gesten und sichert diese international ab. Das Ergebnis ist MoviA - die 'Mobile virtuelle Absich...
The exponential increase in cybercrimes in the past decade has raised new issues and challenges for law and law enforcement. Based on case studies drawn from her work as a lawyer, Susan W. Brenner identifies a diverse range of cybercrimes, including crimes that target computers (viruses, worms, Trojan horse programs, malware and DDoS attacks) and crimes in which the computer itself is used as a tool (cyberstalking, cyberextortion, cybertheft, and embezzlement). Illuminating legal issues unique t...
Computer Science Student ... Sticks and Stones May Break My Bones But Spreadsheets Will Never Hurt Me
by Studygo Official
Sustainable Language Support Practices in Science Education: Technologies and Solutions presents cases on the results of a study done in Australia on first-year university students and the impact of new techniques of language acquisition on science education. The project covered biology, chemistry and physics. Nearly 3,400 students were involved in the project, drawn from the University of Canberra, the University of Technology, Sydney, the University of Sydney, the University of Tasmania and th...
This book constitutes the refereed proceedings of the Third International Conference on Advanced Data Mining and Applications, ADMA 2007, held in Harbin, China in August 2007. The papers focus on advancements in data mining and peculiarities and challenges of real world applications using data mining.
AI Knowledge Transfer from the University to Society
AI Knowledge Transfer from the University to Society: Applications in High-Impact Sectors brings together examples from the "Innovative Ecosystem with Artificial Intelligence for Andalusia 2025" project at the University of Seville, a series of sub-projects composed of research groups and different institutions or companies that explore the use of Artificial Intelligence in a variety of high-impact sectors to lead innovation and assist in decision-making. Key Features Includes chapters on heal...
Lernen Sie mit diesem Buch die Grundlagen der Virtuellen und Augmentierten Realitat kennen Dieses Buch uber die Virtuelle und Augmentierte Realitat ist sowohl fur Praktiker und Interessierte im Selbststudium als auch fur Studierende geeignet. Letztere koennen es hervorragend als Begleitlekture fur entsprechende Lehrveranstaltungen, zum Beispiel in der Informatik nutzen. Die zweite Auflage wurde umfassend erneuert und erweitert. Mit ihrer Hilfe kann der Leser sein Verstandnis fur das Themengebiet...
Multimodal Signal Processing
Multimodal signal processing is an important research and development field that processes signals and combines information from a variety of modalities - speech, vision, language, text - which significantly enhance the understanding, modelling, and performance of human-computer interaction devices or systems enhancing human-human communication. The overarching theme of this book is the application of signal processing and statistical machine learning techniques to problems arising in this multi...
Building Chatbots with Microsoft Bot Framework and Node.Js
by G Akshay Kulkarni
Community Informatics Design Applied to Digital Social Systems (Translational Systems Sciences, #12)
by Pierre-Leonard Harvey
This book introduces a Digital Social System Praxis Framework (DSSPF) integrating Computational Media, Evolutionary Systems Thinking and Design Thinking approaches to E-transformation practice, also called Community Informatics Design (CID). The DSSPF framework is intended to create communication spaces dedicated to knowledge production and sharing for social and organizational change. It allows social systems researchers and practitioners to recognize their synergistic roles in the praxis proce...
AI for Healthcare Robotics (AI for Everything)
by Eduard Fosch-Villaronga and Hadassah Drukarch
Provides for the first time a comprehensive, state-of-the-art overview of the different types of healthcare robots and the advances that AI brings them.Provides, in an easy and accessible way, essential basic information about the autonomy levels of surgery robots, which is novel. As such, could be very valuable to a broad community that ranges from legal scholars, ethicists, developers, policymakers, students, or non-specialists curious about the topic.
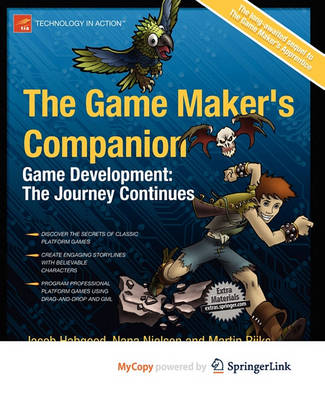
The Game Maker's Companion (Technology in Action)
by Jacob Habgood, Nana Nielsen, and Kevin Crossley
The Game Maker's Companion is the long-awaited sequel to The Game Maker's Apprentice. This book picks up where the last book left off, advancing your game development journey with some seriously impressive gaming projects. This time you'll learn how to make professional-quality platform games with solid collision detection and slick control mechanisms and you'll get acquainted with a long-lost icon of platform gaming history on the way. You'll go on to discover techniques to add depth and believ...