Blockchain, Big Data and Machine Learning
Present book covers new paradigms in Blockchain, Big Data and Machine Learning concepts including applications and case studies. It explains dead fusion in realizing the privacy and security of blockchain based data analytic environment. Recent research of security based on big data, blockchain and machine learning has been explained through actual work by practitioners and researchers, including their technical evaluation and comparison with existing technologies. The theoretical background and...
Control Theory of Nonlinear Mechanical Systems (Oxford Engineering Science, #49)
by Suguru Arimoto
This book introduces a new framework for non-linear analysis and control of intelligent machines such as robot arms, mechanical hands, and other advanced mechatronic systems. It clarifies the physical and mathematical prinicples underlying the complicated dynamics of non-linear mechanical systems and deals with the design of controllers that enable sophisticated tasks to be executed. A new concept called `non-linear position-dependent circuits' plays a crucial role, together with passivity ana...
Cyber–physical Systems: Theory, Methodology and Applications (IEEE Press)
by Pedro H. J. Nardelli
CYBER-PHYSICAL SYSTEMS Provides a unique general theory of cyber-physical systems, focusing on how physical, data, and decision processes are articulated as a complex whole Cyber-physical systems (CPS) operate in complex environments systems with integrated physical and computational capabilities. With the ability to interact with humans through variety of modalities, cyber-physical systems are applied across areas such as Internet of Things (IoT)-enabled devices, smart grids, autonomous auto...
Since the introduction and proliferation of the Internet, problems involved with maintaining cybersecurity has grown exponentially, and have evolved into many forms of exploitation. Yet, Cybersecurity has had far too little study and research. Virtually all of the Research that has taken place in cybersecurity over many years, has been done by those with computer science, electrical engineering, and mathematics backgrounds. However, many cybersecurity researchers have come to realize that to...
System Und Subjekt (Wissenschaftstheorie, Wissenschaft Und Philosophie, #36)
by Axel Ziemke
1. "Wir erzeugen die Welt, in der wir leben, indem wir sie leben". Ausgehend von seiner Biologie der Kognition deutet H.Maturana mit dieser Aussage den in dieser Theorie konzeptualisierten grundsatzlichen Wandel von Wirklichkeitsbegriff und Menschenbild an. Auf der Basis einer Theorie autopoietischer Systeme erarbeitete er eine Alternative zu einem Wirklichkeitsbegriff, der wesentlich durch die Wissenschaft der Neuzeit mit ihrem Anspruch der objektiven Erkenntnis einer von den "Wirk- ursachen" b...
Ethics in Information Technology (Cognitive Approaches in Cloud and Edge Computing.)
by G K Awari and Sarvesh V. Warjurkar
This reference text introduces concepts of computer and Internet crime, ethics in information technology, and privacy techniques. It comprehensively covers important topics including ethical consideration in decision making, security attacks, identification of theft, strategies for consumer profiling, types of intellectual property rights, issues related to intellectual property, process and product quality, software quality assurance techniques, elements of an ethical organization, telemedicin...
Essays in Control (Progress in Systems and Control Theory, Vol 14)
The acquisition of knowledge about systems and the processing of information about them are key features of modern control engineering technology. This is the theme for a volume of articles setting out the scope and content to be covered at the European Control Conference (ECC '93) in Groningen, the Netherlands. The book provides a broad overview of the field of control and a discussion of its development both from a theoretical and an engineering perspective. It contains the fully developed art...
This book provides state-of-the-art scientific and engineering research findings and developments in the area of mobile robotics and associated support technologies. The book contains peer reviewed articles presented at the CLAWAR 2008 conference. Robots are no longer confined to industrial manufacturing environments with a great deal of interest being invested in the use of robots outside the factory environment. The CLAWAR conference series, established as a high profile international event, a...
Innovations and Approaches for Resilient and Adaptive Systems
Innovations and Approaches for Resilient and Adaptive Systems is a comprehensive collection of knowledge on increasing the notions and models in adaptive and dependable systems. This book aims to enhance the awareness of the role of adaptability and resilience in system environments for researchers, practitioners, educators, and professionals alike.
Security and Organization within IoT and Smart Cities
by Kayhan Zrar Ghafoor, Kevin Curran, Linghe Kong, and Ali Safaa Sadiq
This book aims to provide the latest research developments and results in the domain of AI techniques for smart cyber ecosystems. It presents a holistic insight into AI-enabled theoretic approaches and methodology in IoT networking, security analytics using AI tools and network automation, which ultimately enable intelligent cyber space. This book will be a valuable resource for students, researchers, engineers and policy makers working in various areas related to cybersecurity and privacy for S...
Crime Science and Digital Forensics
This volume is a collation of articles on counter forensics practices and digital investigative methods from the perspective of crime science. The book also shares alternative dialogue on information security techniques used to protect data from unauthorised access and manipulation. Scandals such as those at OPCW and Gatwick Airport have reinforced the importance of crime science and the need to take proactive measures rather than a wait and see approach currently used by many organisations. T...
Qualitative Theory of Control Systems (Translations of Mathematical Monographs)
This book analyzes control systems using results from singularity theory and the qualitative theory of ordinary differential equations. The main part of the book focuses on systems with two-dimensional phase space. The study of singularities of controllability boundaries for a typical system leads to the classification of normal forms of implicit first-order differential equations near a singular point. Davydov indicates several applications of these normal forms. The book is accessible to gradu...
Law, Policy, and Technology
Law, Policy, and Technology: Cyberterorrism, Information Warfare, and Internet Immobilization provides relevant frameworks and best practices as well as current empirical research findings in the area. It is aimed at professionals who want to improve their understanding of the impact of cyber-attacks on critical infrastructures and other information systems essential to the smooth running of society, how such attacks are carried out, what measures should be taken to mitigate their impact and wha...
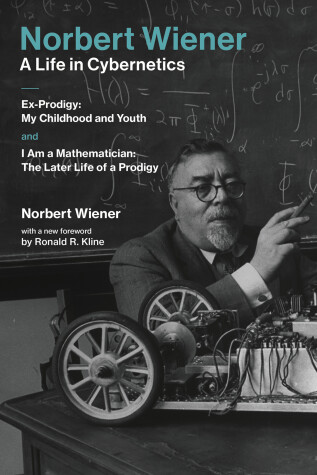
Norbert Wiener's celebrated autobiography, available for the first time in one volume.Norbert Wiener—A Life in Cybernetics combines for the first time the two volumes of Norbert Wiener's celebrated autobiography. Published at the height of public enthusiasm for cybernetics—when it was taken up by scientists, engineers, science fiction writers, artists, and musicians—Ex-Prodigy (1953) and I Am a Mathematician (1956) received attention from both scholarly and mainstream publications, garnering rev...