In the real world there are people who enter the homes and steal everything they find valuable. In the virtual world there are individuals who penetrate computer systems and "steal" all your valuable data. Just as in the real world, there are uninvited guests and people feel happy when they steal or destroy someone else's property, the computer world could not be deprived of this unfortunate phenomenon. It is truly detestable the perfidy of these attacks. Cybercrime is a phenomenon of our time,...
Im Spannungsfeld zwischen informationeller Selbstbestimmung und öffentlicher Sicherheit
by Julian Muller
Passwort Notizbuch (Notizbucher Fur Hundeliebhaber, #9) (Notizbucher Fur Pferdeliebhaber, #4)
by Handliche Notizbucher
Social Media and Address Book Two Zero Two District of Columbia
by Gray Lenox Journals and Notebooks
Email Password Book With Tabs (Email Password Book with Tabs, #1)
by Password Logbook and Internet Addres Uk
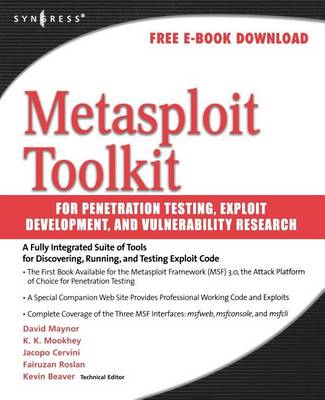
This is the only book that provides integrated, comprehensive, up-to-date coverage of Internet-based security tools and applications. In this age of universal electronic connectivity, viruses and hackers, electronic eavesdropping, and electronic fraud, security is paramount. Network Security: Applications and Standards, 5/e provides a practical survey of network security applications and standards, with an emphasis on applications that are widely used on the Internet and for corporate networks....
Security Fundamentals for E-Commerce (Artech House Computer Security)
by Vesna Hassler
This handbook offers an in-depth understanding of basic security problems and relevant solutions for those charged with maintaining the security of e-commerce sites. From designing secure Web, e-commerce and mobile commerce applications, to securing your internal network, to providing secure employee/user authentication, this book is structured to provide a comprehensive overview or help the reader pinpoint topics of immediate concern.
Small Password Book Alphabetical Tabs (Small Password Book Alphabetical Tabs, #1)
by Password Logbook and Intern Publication
The Official (ISC)2 CCSP CBK Reference, 3rd Edition
by Leslie Fife, Aaron Kraus, and Bryan Lewis