Password Log Book Large Print (Password Log Book Large Print, #1)
by Password Logbook and Internet Ad Portal
The Hacker-Proof Internet Address Password Book - Summer Lake (Personal Internet Address & Password Logbooks, #11)
by Atlantic Journals
Pass Word Manager (Pass Word Manager, #1)
by Password Logbook and Internet Add Press
Password Journal For Girls (Password Journal for Girls, #1)
by Password Logbook and Internet Ad Portal
Android Hacker's Handbook
by Joshua J Drake, Zach Lanier, Collin Mulliner, Pau Oliva Fora, Stephen A Ridley, and Georg Wicherski
The first comprehensive guide to discovering and preventing attacks on the Android OS As the Android operating system continues to increase its share of the smartphone market, smartphone hacking remains a growing threat. Written by experts who rank among the world's foremost Android security researchers, this book presents vulnerability discovery, analysis, and exploitation tools for the good guys. Following a detailed explanation of how the Android OS works and its overall security architecture...
Password Notebook Alphabetical (Password Notebook Alphabetical, #1)
by Password Logbook and Internet Addre USA
Password Notebook Small (Password Notebook Small, #1)
by Password Logbook and Internet Add Press
This book is a step-by-step, practical tutorial for analyzing and detecting malware and performing digital investigations. This book features clear and concise guidance in an easily accessible format. Cuckoo Malware Analysis is great for anyone who wants to analyze malware through programming, networking, disassembling, forensics, and virtualization. Whether you are new to malware analysis or have some experience, this book will help you get started with Cuckoo Sandbox so you can start analysing...
Password Logbook Not to Open
by Password Journal and Internet Password Notebook
An urgently needed examination of the current cyber revolution that draws on case studies to develop conceptual frameworks for understanding its effects on international order The cyber revolution is the revolution of our time. The rapid expansion of cyberspace in society brings both promise and peril. It promotes new modes of political cooperation, but it also disrupts interstate dealings and empowers subversive actors who may instigate diplomatic and military crises. Despite significant expe...
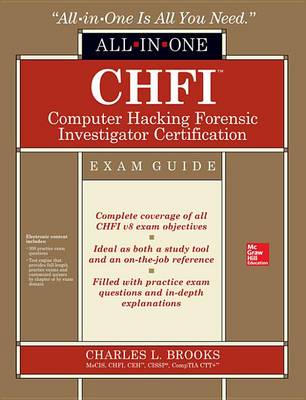
Chfi Computer Hacking Forensic Investigator Certification All-In-One Exam Guide
by Charles L Brooks
Internet Address & Password Log Book
by LLC Internet Address and Password Book
The Internet Book, Fifth Edition explains how computers communicate, what the Internet is, how the Internet works, and what services the Internet offers. It is designed for readers who do not have a strong technical background — early chapters clearly explain the terminology and concepts needed to understand all the services. It helps the reader to understand the technology behind the Internet, appreciate how the Internet can be used, and discover why people find it so exciting. In addition, it...
Pass Word Keeper (Pass Word Keeper, #1)
by Password Logbook and Internet Ad Portal