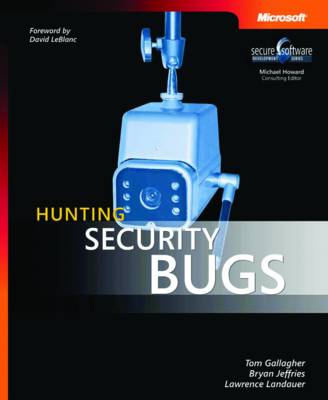
Learn how to think like an attacker—and identify potential security issues in your software. In this essential guide, security testing experts offer practical, hands-on guidance and code samples to help you find, classify, and assess security bugs before your software is released. Discover how to: Identify high-risk entry points and create test cases Test clients and servers for malicious request/response bugs Use black box and white box approaches to help reveal security vulnerabilities Unco...
An explanation of the five pillars or battlefields of Cybersecurity and how a Zero Trust approach can change the advantage on each battlefield. Deep dive into each of five battlefields where we have a decided disadvantage due to constitutional structure and moral behavioural guidelines and examples of how we got here, and what we can do about it, and moreover why we got here and how we can avoid those traps in the future. A unique viewpoint that has never been explored – five battlefields includ...
Technology has become deeply integrated into modern society and various activities throughout everyday life. However, this increases the risk of vulnerabilities, such as hacking or system errors, among other online threats. Cybersecurity Breaches and Issues Surrounding Online Threat Protection is an essential reference source for the latest scholarly research on the various types of unauthorized access or damage to electronic data. Featuring extensive coverage across a range of relevant perspect...
Organizations of all sizes struggle to secure their data in a constantly evolving digital landscape. Expanding digital footprints and the rapid expansion of cloud strategies arising from the COVID-19 pandemic increase an organization’s attack surface. When combined with limited resources caused by the cybersecurity skills gap, securing small and mid-sized business IT infrastructures becomes more complicated. With limited staffing and budgetary restrictions, small businesses need to create cost-e...
Cybersecurity for Beginners (How to Get a Job in Cybersecurity, #2) (2 Manuscripts, #3)
by Attila Kovacs
A cybersecurity expert and former FBI “ghost” tells the thrilling story of how he helped take down notorious FBI mole Robert Hanssen, the first Russian cyber spy. “Both a real-life, tension-packed thriller and a persuasive argument for traditional intelligence work in the information age.”—Bruce Schneier, New York Times bestselling author of Data and Goliath and Click Here to Kill Everybody Eric O’Neill was only twenty-six when he was tapped for the case of a lifetime: a one-on-one undercover...
How to protect yourself from adware and spyware
by Luis Paulo Soares
This book will educate readers on the need for application security and secure coding practices when designing any app. No prior knowledge of security or secure programming techniques is assumed. The book will discuss the need for such practices, how the Android environment is structured with respect to security considerations, what services and techniques are available on the platform to protect data, and how developers can build and code applications that address the risk to their applications...
Common Windows, Linux and Web Server Systems Hacking Techniques
by Hedaia Mahmood Al-Assouli